Learn More About Business Security Solutions for Enterprises
Introduction to Business Security Solutions
In today’s fast-paced and technology-driven world, businesses face a myriad of security challenges. Whether it’s safeguarding sensitive data, protecting physical assets, or ensuring the safety of employees, comprehensive security solutions are crucial for modern enterprises. As companies increasingly rely on digital infrastructure and interconnected systems, the need for robust security measures has never been more apparent. This article explores the various facets of business security solutions, providing insights into how they can help protect data, staff, and assets, ultimately supporting long-term business continuity.
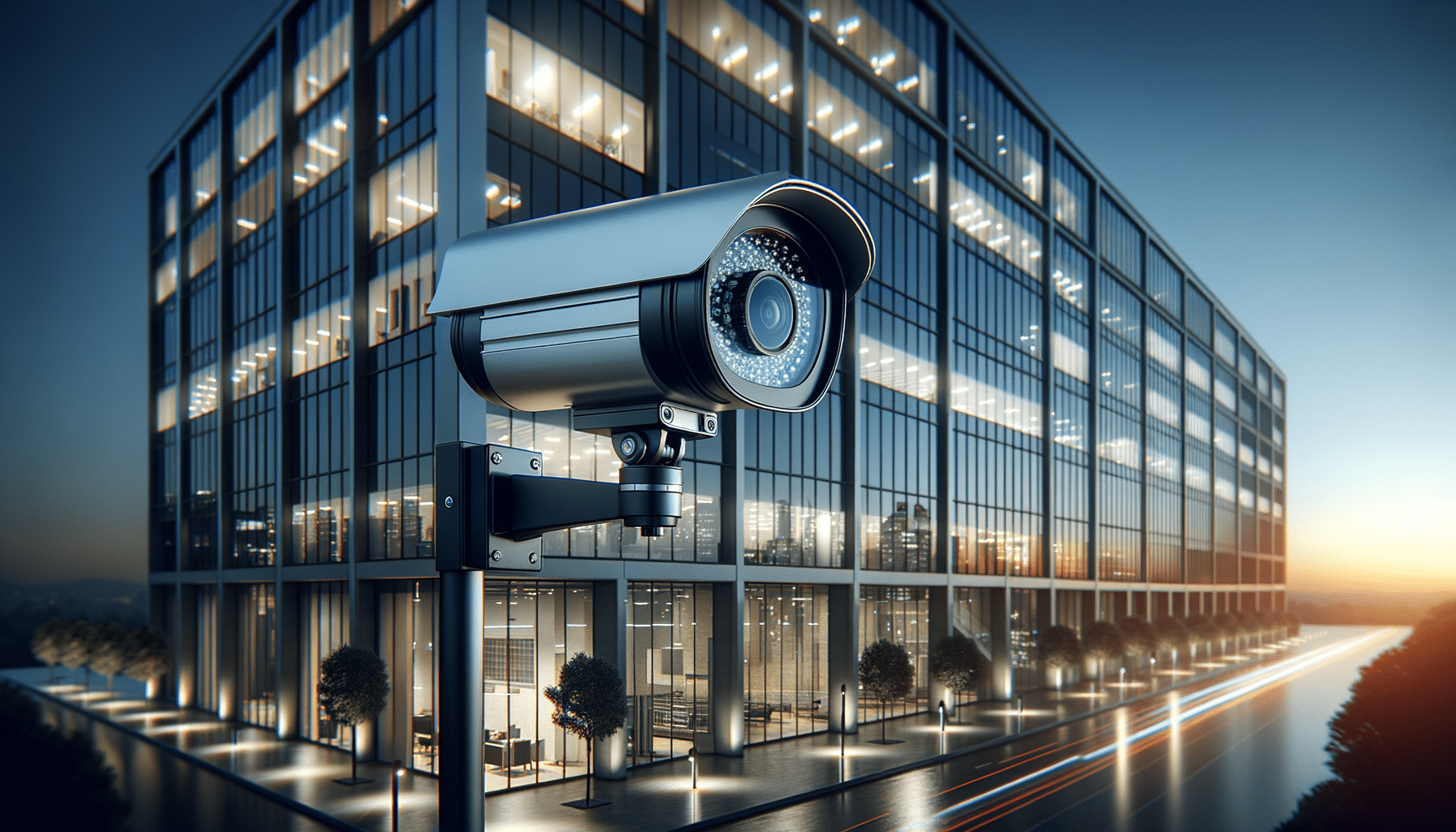
Understanding Surveillance Systems
Surveillance systems are a cornerstone of business security, providing a watchful eye over operations and deterring potential threats. These systems often include a combination of cameras, sensors, and monitoring software, each playing a vital role in maintaining security. Modern surveillance solutions offer high-definition video, night vision capabilities, and remote access, allowing businesses to monitor their premises 24/7.
One of the significant advancements in this field is the integration of artificial intelligence (AI) and machine learning. These technologies enhance surveillance systems by enabling features such as facial recognition, anomaly detection, and automated alerts. For instance, AI can analyze video feeds in real-time to identify suspicious activities, reducing the reliance on human operators and improving response times.
Businesses can tailor their surveillance setups to meet specific needs, whether it’s monitoring a single location or managing multiple sites. By investing in advanced surveillance solutions, companies can not only protect their assets but also gain valuable insights into operational efficiencies and customer behaviors.
Implementing Access Control Systems
Access control systems are essential for regulating who can enter and exit specific areas within a business. These systems range from simple lock-and-key mechanisms to sophisticated biometric scanners and card access systems. By controlling access, businesses can prevent unauthorized entry, safeguard sensitive information, and enhance overall security.
Modern access control solutions often incorporate smart technology, allowing for seamless integration with other security systems. For example, access logs can be linked to surveillance footage, providing a comprehensive view of who accessed a particular area and when. This integration is particularly beneficial for industries that handle sensitive data or valuable assets, such as finance or healthcare.
Furthermore, access control systems can be customized to fit the unique requirements of a business. Whether it’s setting different access levels for employees or enabling temporary access for visitors, these systems offer flexibility and scalability. By implementing robust access control measures, businesses can create a secure environment that fosters trust and compliance.
The Role of Cybersecurity in Business Security
With the increasing reliance on digital technologies, cybersecurity has become an integral part of business security solutions. Cyber threats such as data breaches, ransomware attacks, and phishing scams can have devastating effects on a company’s reputation and financial standing. Therefore, safeguarding digital assets is as crucial as protecting physical ones.
Effective cybersecurity strategies involve a combination of tools, policies, and practices designed to prevent, detect, and respond to cyber threats. Key components include firewalls, antivirus software, encryption, and regular security audits. Additionally, employee training programs can play a vital role in enhancing cybersecurity, as human error is often a significant factor in security breaches.
Businesses must stay informed about the latest cyber threats and continuously update their security measures to combat evolving risks. By prioritizing cybersecurity, companies can protect their digital infrastructure and maintain the trust of their customers and partners.
Integrating Security Solutions for Comprehensive Protection
To achieve comprehensive protection, businesses must integrate various security solutions into a cohesive system. This approach ensures that all aspects of security work together seamlessly, providing a robust defense against potential threats. Integration can be achieved through centralized management platforms that allow for real-time monitoring and control of all security components.
For instance, a centralized security platform can link surveillance systems with access control and cybersecurity measures, enabling businesses to respond quickly to incidents. Automated alerts and reporting features enhance situational awareness and facilitate informed decision-making.
Furthermore, integrated security solutions can lead to cost savings and operational efficiencies. By reducing the need for multiple standalone systems, businesses can streamline their security operations and allocate resources more effectively. Ultimately, a well-integrated security system not only safeguards assets but also supports business growth and resilience.